title="Encrypted Messaging for Anarchists"
date=2023-04-02
[taxonomies]
categories = ["Defensive"]
tags = ["intro", "e2ee", "easy"]
[extra]
blogimage="/images/BASE_2.png"
toc=true
dateedit=2023-05-10
a4="e2ee-a4.pdf"
letter = "e2ee-letter.pdf"There are several different options for end-to-end encrypted communication, each with different trade-offs. This article provides an overview and installation instructions for Tails, Qubes OS, and GrapheneOS.
Before proceeding, there are a few concepts that need to be understood, in order to distinguish between the various options.
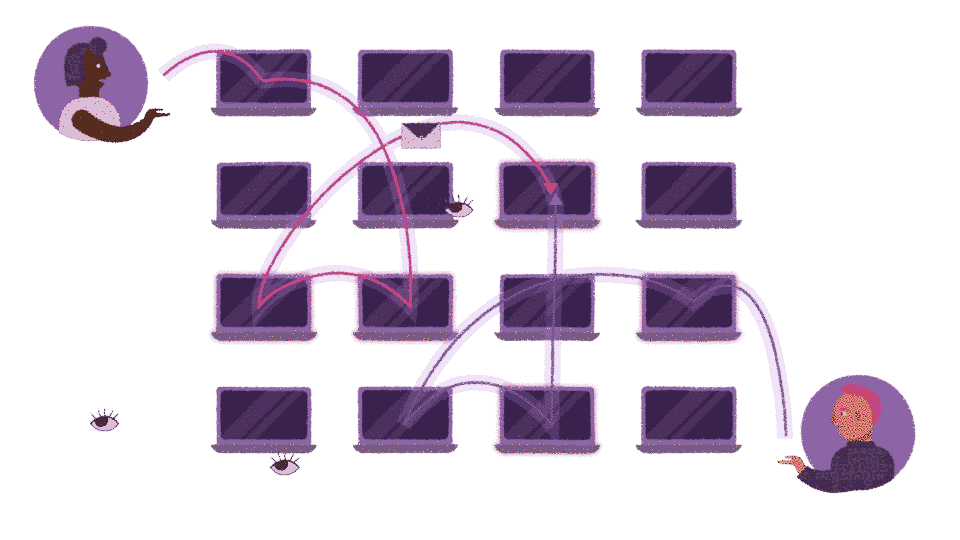
- End-to-end encryption means that only you and the person you are communicating with can read messages. However, not all encryption is created equal. The quality of the encryption is determined by the encryption protocol used and how it is implemented at the software level.
- Metadata protection means that the metadata (the data about the data) about the communication is obscured. Even if the message itself is encrypted, metadata can reveal who is communicating with whom, when, how often, the sizes of any files that may have been transferred, and so on. Metadata exposure is a major concern.
- Peer-to-peer means that there is no centralized server to trust.
- Tor is an anonymity network, and some applications route your messages through it by default.
For a more in-depth look at these various considerations, we recommend The Guide to Peer-to-Peer, Encryption, and Tor: New Communication Infrastructure for Anarchists. This text criticizes Signal for not being peer-to-peer and not using Tor by default, and goes on to compare Signal, Cwtch, and Briar.
The following options for encrypted messaging are listed from most metadata protection to least.
TLDR: Use Cwtch. Don't use Signal or PGP.
Cwtch
- Mediums: Text
- Metadata protection: Yes (strong)
- Encryption protocol: Tor Onion Services (v3) + Tapir
- Peer-to-peer: Yes
- Tor: Yes
Cwtch is our preference, by a long shot. It is currently transitioning from beta to stable versions. For an overview of how Cwtch works, watch the video above. The Cwtch Handbook will tell you everything you need to know to use it. Cwtch is designed with metadata protection in mind; it is peer-to-peer, uses the Tor network as a shield, and stores everything locally on the device, encrypted.
Like all peer-to-peer communication, Cwtch requires synchronous communication, meaning that both peers must be online at the same time. However, its server feature also allows asynchronous communication by providing offline delivery:
"Cwtch contact to contact chat is fully peer to peer, which means if one peer is offline, you cannot chat, and there is no mechanism for multiple people to chat. To support group chat (and offline delivery) we have created untrusted Cwtch servers which can host messages for a group. [...] the server has no way to know what messages for what groups it might be holding, or who is accessing it."
Any Cwtch user can turn the app on their phone or computer into an untrusted server to host a group chat, though this is best for temporary needs like an event or short-term coordination, as the device must remain powered on for it to work. Once the server exists, contacts can be invited to use it. You can create a group chat with only two people, allowing for asynchronous direct messaging. If an adversary gets access to a server running on your own device in addition to an invitation to join the server, they can deanonymize you. Fortunately, both Systemli and Anarchy Planet run public servers that are suitable for long-term groups and can't be used to deanonymize you.
Asynchronous conversations on Cwtch need to be started from a synchronous conversation - you need to be online at the same time as your contact to invite them to a group, and then you no longer need to be online at the same time. In the future, Cwtch plans to improve this with hybrid groups. Until hybrid groups are implemented, you will need to establish your asynchronous Cwtch conversations by using a second channel to set a time for when you both need be online.
Note
Briar is another application that works in a similar way (with peer-to-peer and Tor), using the Bramble Transport Protocol (BTP). Briar's main distinguishing feature is that it continues to work even when the underlying network infrastructure is down. It was audited in 2017. Unfortunately, Briar Desktop does not yet work with Tails or Qubes-Whonix because it cannot use the system Tor. Unlike Cwtch, to connect to a contact on Briar, you both have to add each other first. You can either exchange
briar://links or scan a contact’s QR code if they are nearby. Briar Mailbox allows asynchronous communication.
Cwtch Installation on GrapheneOS
If you have decided to use a smartphone despite our recommendation not to use phones, Cwtch is available for Android. Follow the instructions for installing software that isn't available in the Play Store. Updates must be done manually - back up your profile first.
Cwtch Installation on Tails
Cwtch is still in beta - support for Tails is very new and not thoroughly tested.
- Start Tails with an Adminstration Password.
- Download Cwtch for Linux with Tor Browser
- Verify your download
- Open the folder using the Tor Browser's download icon
- Right-click in the file manager and select "Open a Terminal Here"
- Run
sha512sum cwtch-VERSION-NUMBER.tar.gz(replace the version number as appropriate) - Compare the hash of the file to what is listed on the download page
- According to our Tails Best Practices, personal data should be stored on a second LUKS USB and Persistent Storage should not be enabled. Extract the file with the file manager (right click, select "Extract Here"), then copy the
cwtchfolder to such a personal data LUKS USB.- OPTIONAL - If you enable Persistent Storage: with Persistent Storage unlocked, in Terminal run
sudo sed -i '$ a /home/amnesia/.cwtch source=cwtch' /live/persistence/TailsData_unlocked/persistence.conf && sudo sed -i '$ a /home/amnesia/.local source=cwtch_install' /live/persistence/TailsData_unlocked/persistence.confthen restart Tails for the changes to take effect, again with an Adminstration Password.
- OPTIONAL - If you enable Persistent Storage: with Persistent Storage unlocked, in Terminal run
- Run the install script
- In the File Manager, browse to the directory you just created,
cwtch. Right click in the File Manager and select "Open a Terminal Here" - Run
install-tails.shand enter the Administration Password when prompted.
- In the File Manager, browse to the directory you just created,
- As the documentation states, "When launching, Cwtch on Tails should be passed the CWTCH_TAILS=true environment variable". In the Terminal, run:
exec env CWTCH_TAILS=true LD_LIBRARY_PATH=~/.local/lib/cwtch/:~/.local/lib/cwtch/Tor ~/.local/lib/cwtch/cwtch
- With Persistent Storage disabled, configuration and profile data must be restored from backup every session you need to install Cwtch. Backup
/home/amnesia/.cwtch/to the personal data LUKS USB, and copy it back to/home/amnesia/the next time you install Cwtch. - Updates to new versions must be done manually - back up your profile first.
OnionShare
- Mediums: Text
- Metadata protection: Yes (strong)
- Encryption protocol: Tor Onion Services (v3)
- Peer-to-peer: Yes
- Tor: Yes
OnionShare has a chat feature that creates an ephemeral peer-to-peer chat room that is routed over the Tor network. The metadata protection works in the same way as Cwtch; it uses the Tor network as a shield and stores everything (ephemerally) locally on the device. The encryption protocol is the Tor v3 onion service encryption; elliptic curve Diffie Hellman with Curve25519. Cwtch and Briar both have more features (including the additional Tapir and BTP encryption protocols). The only advantage of OnionShare is that it is installed on Tails by default.
Signal
- Mediums: Video call, voice call, text
- Metadata protection: Yes (Moderate)
- Encryption protocol: Signal Protocol, audited (2017)
- Peer-to-peer: No
- Tor: Not default
The Signal Protocol has a moderate amoung of metadata protection; sealed sender, private contact discovery, and the private group system. Message recipient identifiers are only stored on Signal's servers for as long as it takes to deliver each message. As a result, if Signal is served with a warrant, they will only be able to provide the time of account creation and the date of the account's last connection to the Signal servers. Still, Signal relies on the Google Services Framework (though it's possible to use it without it), and the sealed sender metadata protection applies only to contacts (by default).
Signal is not peer-to-peer; it uses centralized servers that we must trust. Signal will work with Tor if used on an operating system that forces it to, such as Whonix or Tails.
Signing up for a Signal account is difficult to do anonymously. The account is tied to a phone number that the user must still control - due to changes in "registration lock", it is no longer sufficient to register with a disposable phone number. An anonymous phone number can be obtained on a burner phone or online and must be maintained - most people will not do this. There have been unfounded rumors that Signal plans to remove the need for a phone number after the release of a username feature - however, registration will still require a phone number.
Another barrier to anonymous registration is that Signal Desktop will only work if Signal is first registered from a smartphone. For users familiar with the command line, it is possible to register an account from a computer using Signal-cli. The VoIP account used for registration would have to be obtained anonymously.
These barriers to anonymous registration mean that Signal is rarely used anonymously. This has significant implications if the State gains physical or remote access to the device. One of the primary goals of State surveillance of anarchists is network mapping, and it's common for them to gain physical access to devices through house raids or even simple arrests. For example, if your device's authentication is bypassed, it would be possible to identify each of your Signal contacts simply by their phone number (in addition to reading message history, etc.). This is a serious security breach, especially in the context of Signal groups, and is unavoidable due to the way Signal is designed. Compare this to the same attack on a Cwtch user - all contacts are anonymous, and their identities are also protected by Tor, so device compromise does not contribute to network mapping.
Simply put, Signal does not fit an anarchist threat model - it was designed to bring encrypted communication to the masses. Because it's nearly impossible to use Signal anonymously, and because we recommend against using phones, we recommend that anarchists don't use Signal. We only provide installation instructions because it has become the norm in the anarchist space in many countries, and it may be difficult to contact someone without it.
Signal Installation on GrapheneOS
If you have decided to use a smartphone despite our recommendation not to use phones, we recommend the Signal Configuration and Hardening Guide. As noted above, unless you are familiar with the Command Line Interface, Signal needs to be registered on a smartphone before it can be connected to a computer. Install Signal as you would any app that doesn't require Google Services (we don't recommend F-Droid).
Molly-FOSS is a fork of Signal with hardening and anti-forensic features available on Android - we recommend it over Signal for anarchists, and extending trust to the Molly team is made easier by its reproducible builds. Follow the instructions for installing software that isn't available in the Play Store. You can migrate from an existing Signal account. Turn on database encryption.
Signal Installation on Tails
About.Privacy maintains a guide for installing Signal Desktop on Tails. There is a guide for registering an account from Tails without a smartphone (using Signal-cli), and another guide for if you already have a Signal account.
Some of the Signal Configuration and Hardening Guide also applies to Signal Desktop.
Signal Installation on Qubes-Whonix
Signal Desktop on Whonix is not guaranteed to have Tor Stream Isolation from other applications in the same qube, so we will install it in a dedicated qube. Signal Desktop is installed in a Template, not an App qube (because it is available as a .deb from a third party repository).
Some of the Signal Configuration and Hardening Guide also applies to Signal Desktop.
- Go to Applications menu → Qubes Tools → Qube Manager
- Clone whonix-ws-16 and name it something like whonix-ws-16-signal.
- We do this so as not to add attack surface to the base Whonix Workstation template. If you also install other messaging applications like Element Desktop, they could share a cloned template with a name like whonix-ws-16-e2ee
- Open a Terminal in the new Template: Applications menu → Template: whonix-ws-16-signal: Xfce Terminal
- Run the commands in the Signal installation guide to install Signal Desktop in the Template.
- Note that the layout of the Signal installation guide is a bit confusing for users unfamiliar with the command line;
wgetandcatare separate commands, butechoin #2 is a command so long that it takes two lines (which is why the second line is indented). - Template qubes require a proxy for
wget. Before running the command, create a configuration file at~/.wgetrcin the Template, with the following contents:
- Note that the layout of the Signal installation guide is a bit confusing for users unfamiliar with the command line;
use_proxy = on
http_proxy = 127.0.0.1:8082
https_proxy = 127.0.0.1:8082-
Create an App qube with the Template
whonix-ws-16-signaland networkingsys-whonix. - In the Settings → Applications tab of the new App qube, move Signal to the Selected column and press OK.
- Updates will be handled by Qubes Update as you would expect.
Alternative method
You can install Signal Desktop in a Whonix Workstation App qube using Qube Apps and not need to bother with Templates. Signal Desktop on Flathub is community maintained, not official, which is a security consideration.
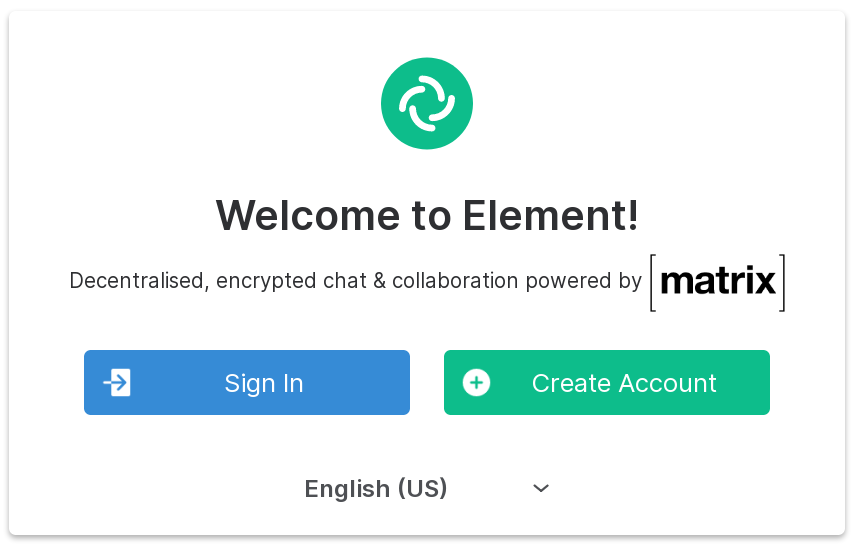
Element / Matrix
- Mediums: Video call, voice call, text
- Metadata protection: Poor
- Encryption protocol: vodozemac, audited (2022)
- Peer-to-peer: No
- Tor: Not default
Element is the name of the application (the client) and Matrix is the name of the network. A comparison to email may be helpful in understanding this; Element is the equivalent of Thunderbird, while Matrix is the equivalent of the Simple Mail Transfer Protocol (SMTP) that underlies email. Element/Matrix is not peer-to-peer; you have to trust the server. However, unlike Signal, the servers are not centralized, but rather federated - anyone can host their own. Unfortunately, the "federation model" has the trade-off that Matrix has no metadata protection: "Federated networks are naturally more vulnerable to metadata leaks than peer-to-peer or centralized networks". To minimize this, see Systemli's notes on the safe use of the Matrix service.
Element will work with Tor when used on an operating system that forces it, such as Whonix or Tails.
Which homeserver you use is important — do not use the default homeserver matrix.org. Systemli and Anarchy Planet are reputable radical hosts. Both have a default message retention time of 30 days and do not store IP addresses.
Matrix can be used through either a web client (using Element Web on Tor Browser) or a desktop client (using Element Desktop). The web clients for Systemli and Anarchy Planet are element.systemli.org and anarchy.chat, respectively. If you are using a desktop client, change the homeserver address to https://matrix.systemli.org or https://riot.anarchyplanet.org before trying to log in. It is easy to create an account anonymously and does not require a phone. Systemli requires you to have an email account with them (for which you need an invitation), while anyone can register at Anarchy Planet using the registration code aplanet.
A matrix ID looks like @username:homeserver, for example @anarsec:riot.anarchyplanet.org. Just like email, you can send messages to accounts that are on different homeservers.
Once you are logged in, go to Settings → Security & Privacy.
- You'll see all the devices you're signed in to listed under Where you're signed in. For anonymous use cases, you will usually only be signed in to one device.
- Scroll down to Secure Backup. This is a feature that allows you to verify a new session without having access to a signed-in device. Press Set up, then Generate a Security Key. Save the Security Key in KeePassXC. This "Security Key" will be needed to log into a new device or session.
- For Element Desktop, you will only need to use the Security Key if you sign out.
- For Element Web (using Tor Browser), you will need the Security Key every time you use it. Tor Browser will clear your cookies, so you will need to sign in for a new session.
Some current limitations
- "Disappearing messages" is not a feature yet, but it is coming. Message retention time can be set by the homeserver administrator, as mentioned above, and is in fact set on both of our recommended homeservers.
- One-to-one audio/video calls are encrypted and you can use them. Group audio/video calls are not encrypted, so don't use them. This will be fixed when Element-call is stable.
- The Matrix protocol itself theoretically supports forward secrecy, but it is not currently supported in Element because it breaks some aspects of the user experience such as key backups and shared message history.
- Profile pictures, reactions, and nicknames are not encrypted.
Note
You may have heard of XMPP (formerly known as Jabber). XMPP has similar security properties to Matrix, but many clients don't support end-to-end encryption (using the OMEMO protocol) by default. Properly configuring a client is non-trivial. XMPP and Matrix leak similar amounts of metadata, but OMEMO has never been formally audited like the Matrix encryption protocol. In addition, the administrator can act as a man-in-the-middle on any XMPP server. For these reasons, we recommend using Matrix instead of XMPP.
Element Installation on GrapheneOS
If you have decided to use a smartphone despite our recommendation not to use phones, Element is available for Android. Install Element as you would any app that doesn't require Google Services (we don't recommend F-Droid).
Element Installation on Tails
The easiest option is to use the Element web client on Tor Browser. It doesn't require any additional software. Tor Browser deletes all data when it closes, so you'll be prompted for the Security Key each time you login in to access your past messages. Be sure to Sign Out when you are finished, to avoid accumulating "Signed-in devices".
To install Element Desktop, About.Privacy maintains a guide.
Element Installation on Qubes-Whonix
The easiest option is to use the Element web client on Tor Browser is a disposable Whonix qube. It doesn't require any additional software. Tor Browser deletes all data when it closes, so you'll be prompted for the Security Key after each time you log in to access your past messages. Be sure to Sign Out when you are finished, to avoid accumulating "Signed-in devices".
To install Element Desktop, Whonix is not guaranteed to have Tor Stream Isolation from other applications in the same qube, so we will install it in a dedicated qube. Element Desktop is installed in a Template, not an App qube (because it is available as a .deb from a third party repository).
- Go to Applications menu → Qubes Tools → Qube Manager
- Clone whonix-ws-16 and name it something like whonix-ws-16-element.
- We do this so as not to add attack surface to the base Whonix Workstation template. If you also install other messaging applications like Signal Desktop, they could share a cloned template with a name like whonix-ws-16-e2ee
- Open a Terminal in the new Template: Applications menu → Template: whonix-ws-16-element: Xfce Terminal
- Run the commands in the Element installation guide to install Element Desktop in the Template.
- Template qubes require a proxy for
wget. Before running the command, create a configuration file at~/.wgetrcin the Template, with the following contents:
- Template qubes require a proxy for
use_proxy = on
http_proxy = 127.0.0.1:8082
https_proxy = 127.0.0.1:8082-
Create an App qube with the Template
whonix-ws-16-elementand networkingsys-whonix. - In the Settings → Applications tab of the new App qube, move Element Desktop to the Selected column and press OK.
- Updates will be handled by Qubes Update as you would expect.
- Avoid pressing "Sign Out", just shut down the qube when finished.
Alternative method
You can install Element Desktop in a Whonix Workstation App qube using Qube Apps and not need to bother with Templates. Element Desktop on Flathub is community maintained, not official, which is a security consideration.
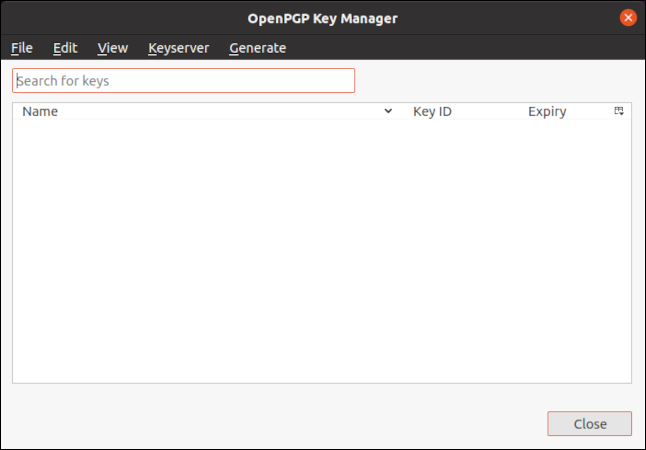
PGP Email
- Mediums: Text
- Metadata protection: No
- Encryption protocol: RSA or ed25519, no forward secrecy
- Peer-to-peer: No
- Tor: Not default
PGP (Pretty Good Privacy) is not so much a messaging platform as it is a way to encrypt messages on top of existing messaging platforms (in this case, email). PGP email does not have the encryption property of forward secrecy. The goal of forward secrecy is to protect past sessions from future key or password compromises. It maintains the secrecy of past communications even if the current communication is compromised. This means that an adversary could decrypt all future PGP messages in one fell swoop. When you also consider the metadata exposure inherent in email, PGP should be disqualified from inclusion on this list. It simply doesn't meet the standards of modern cryptography. However, since it is already widely used in the anarchist space, we include it here as a warning that we recommend that anarchists don't use PGP. For a more technical critique, see The PGP Problem and Stop Using Encrypted Email. Privacy Guides agrees that "email is best used for receiving transactional emails [...], not for communicating with others."
We recommend switching to Cwtch for synchronous and asynchronous use cases. If you must use email, use a radical server and read the Riseup Guide to Encrypted Email.
PGP is used for another purpose outside of communication: verifying the integrity and authenticity of files. For this use case, see our GPG explanation.